Cryptocurrency & Bitcoin
Deep Dive into Blockchain Technology, Digital Currency & Decentralized Finance
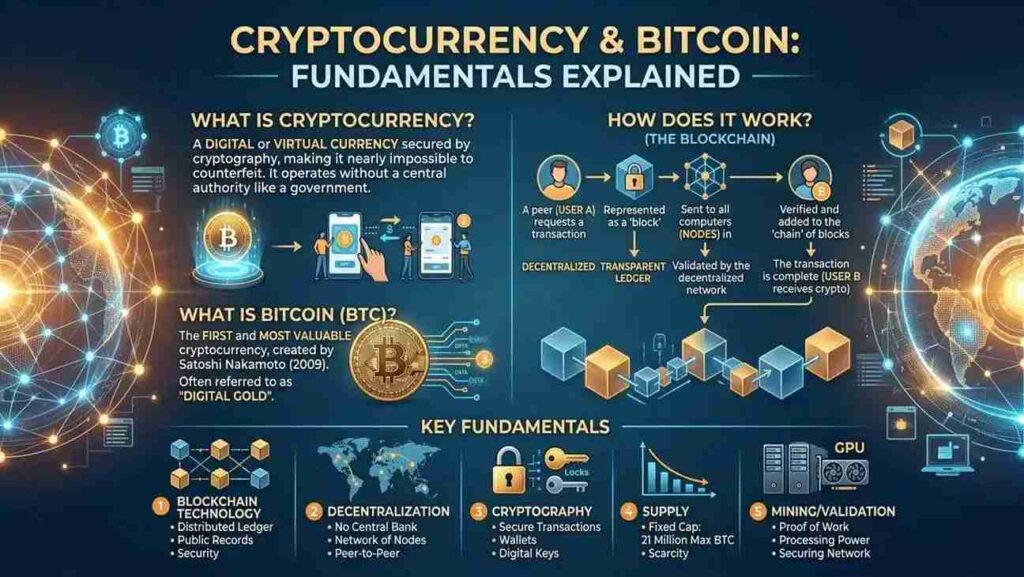
What is Cryptocurrency?
Digital currency secured by cryptography, operating without central authorities
🔐 Cryptography
Uses advanced mathematical algorithms to secure transactions and control creation of new units. Each transaction is encrypted and verified through cryptographic keys.
🌐 Decentralized
Operates on peer-to-peer networks without central banks or governments. Every participant has equal authority and maintains a copy of the transaction ledger.
⛓️ Immutable
Transactions are permanent and cannot be altered or reversed. Once confirmed, they become part of an permanent historical record.
💰 Value Transfer
Enable direct peer-to-peer transactions without intermediaries. Send value anywhere globally instantly with minimal fees.
📊 Transparency
All transactions are visible on the public ledger. Users remain pseudonymous while activity is fully transparent.
🔑 Ownership Control
Users control their funds through private keys. Only the holder can access and transfer their cryptocurrency.
Bitcoin: The First Cryptocurrency
Created in 2009 by Satoshi Nakamoto, Bitcoin revolutionized digital currency
🎯 Purpose
Bitcoin is a peer-to-peer electronic cash system that eliminates the need for trusted third parties like banks. It enables direct value transfer between individuals.
📊 Supply
Maximum supply capped at 21 million Bitcoin. This scarcity mimics precious metals and creates value through limited availability.
⏱️ Block Time
New blocks added approximately every 10 minutes. This consistent rate ensures predictable transaction confirmation times.
💾 Ledger Size
Complete blockchain (~500GB+) contains all transactions since 2009. Anyone can download and verify the entire history independently.
🔗 Consensus
Uses Proof of Work consensus mechanism. Miners compete to solve mathematical puzzles to validate transactions and earn rewards.
🌍 Global Access
Access from anywhere with internet. No geographic restrictions, account requirements, or approval processes needed.
The Blockchain: A Visual Journey
How transactions are linked together in an unbreakable chain
Each block contains the cryptographic hash of the previous block, creating an unbreakable chain. Altering any transaction would change its hash and break the chain for all following blocks.
Block Anatomy: What’s Inside?
Understanding the structure of a single blockchain block
📌 Block Header
The metadata section that identifies and secures the block
Blockchain software version (e.g., version 1.0)
256-bit cryptographic hash of previous block
Hash of all transactions in this block
Unix timestamp of block creation
Current mining difficulty requirement
⛏️ Nonce (Number Used Once)
A number miners change repeatedly to find valid proof of work
Range: 0 to 4,294,967,295 | Required for puzzle solution
📝 Transaction List
All transactions included in this block (typically 1,000s of transactions)
34-character alphanumeric address | Your public key
Recipient’s public address
Value transferred in Bitcoin (₿)
Mining incentive paid by sender (satoshis per byte)
Proof of ownership using private key
✅ Validation & Hashing
The proof that this block is legitimate and part of the chain
SHA-256 Hash of entire block | Must start with specific number of zeros
How Transactions Work
The complete lifecycle of a Bitcoin transaction from creation to confirmation
Create & Sign
You create a transaction specifying the receiver address and amount. You sign it with your private key, proving you own the funds.
Broadcast Network
Your signed transaction is broadcast to all nodes in the network. Each node validates it by checking your signature and confirming you have sufficient funds.
Memory Pool
Valid transactions enter the “mempool” waiting to be mined. Transactions with higher fees get priority and are included in blocks faster.
Miner Selection
Miners select transactions from the mempool to include in the next block. They prioritize high-fee transactions for maximum profit.
Mining Process
Miners solve a complex mathematical puzzle using the block data. The first to solve it gets to add the block to the blockchain and earns the block reward + fees.
Block Added
The new block is added to the blockchain and broadcast to all nodes. Each node verifies the block and updates their copy of the ledger.
Confirmation
As more blocks are added after yours, your transaction becomes more secure. After 6 confirmations (~60 minutes), it’s considered irreversible.
Mining: Securing the Network
How miners validate transactions and earn Bitcoin rewards
⛏️ Computational Work
Miners perform complex SHA-256 hashing calculations. They must find a nonce value that produces a hash meeting the difficulty target (starting with specific number of zeros).
🎯 Difficulty Adjustment
Every 2,016 blocks (~2 weeks), difficulty adjusts to maintain 10-minute block times. More miners = higher difficulty; fewer miners = lower difficulty.
💎 Block Reward
Successfully mining a block earns Bitcoin reward (currently 6.25 BTC) plus all transaction fees in the block. Reward halves every 4 years.
🖥️ Hardware Requirements
Modern mining requires specialized ASIC chips (Application-Specific Integrated Circuits) designed solely for SHA-256 hashing at massive scale.
⚡ Energy Consumption
Bitcoin mining consumes significant electricity to perform trillions of hash calculations. This energy cost is integral to Bitcoin’s security model.
🌍 Mining Pools
Miners join pools to combine computing power. Rewards are shared proportionally to contributed work, reducing variance for individual miners.
Cryptographic Security
The mathematical foundation that makes Bitcoin trustworthy
🔐 Private Key
Your secret key – never share this with anyone
256-bit random number | Controls all funds in associated address | Mathematically generates public key
🔓 Public Key
Derived mathematically from private key using ECDSA
Can be safely shared | Used to receive funds | Proves you signed a transaction
📬 Bitcoin Address
Hash of your public key – what you give to others to receive funds
34-character string | Legacy (P2PKH), SegWit (P2WPKH), or Multi-sig addresses available | Impossible to reverse-engineer private key
✍️ Digital Signature
Mathematical proof that you signed a transaction without revealing private key
ECDSA (Elliptic Curve Digital Signature Algorithm) | Verifiable using public key | Impossible to forge without private key
🔗 Hash Function (SHA-256)
Converts any data into a unique 256-bit fingerprint
Deterministic: same input = same hash | Any change in input completely changes output | One-way: cannot reverse from hash to original data
⛓️ Merkle Tree
Binary tree structure where leaf nodes are transaction hashes
Parent nodes hash their children | Allows verification of any transaction without downloading entire block | Single hash (Merkle Root) represents all transactions
Essential Cryptocurrency Concepts
Terminology and principles you need to understand
💼 Wallet
Software or device storing your private keys and allowing transactions. Not actually storing coins – it stores the keys that prove ownership of blockchain addresses.
🔗 Node
Computer running blockchain software, maintaining a copy of the entire transaction history. Validates transactions and blocks according to consensus rules.
🌳 Full Node
Downloads and validates the entire blockchain. Requires significant storage (~500GB) but provides maximum security and independence.
⚡ Lightning Network
Second-layer payment protocol enabling instant, low-fee transactions. Creates payment channels between users, settling on-chain periodically.
💱 Exchange
Platform where cryptocurrencies are traded for fiat currency or other cryptocurrencies. Requires KYC verification and acts as custodian.
🔄 Consensus Mechanism
Protocol for network participants to agree on blockchain state. Bitcoin uses Proof of Work; other cryptocurrencies use Proof of Stake or alternatives.
📊 HODL
Strategy of holding cryptocurrency long-term rather than trading. Originated from misspelling of “hold” but became community philosophy.
🎯 Smart Contract
Self-executing code on blockchain that automatically enforces terms. Bitcoin supports limited scripting; other platforms (Ethereum) support full programming.
📈 Altcoin
Any cryptocurrency other than Bitcoin. Examples include Ethereum, Litecoin, Ripple. Some improve on Bitcoin’s design; others serve different purposes.
Security & Best Practices
Protecting your cryptocurrency from theft and loss
Private Key Management
Never share your private key with anyone. Store it securely offline. Use hardware wallets for large amounts. Never screenshot or email private keys.
Cold Storage
Keep most holdings offline in “cold storage” (hardware wallets, paper wallets). Use “hot wallets” only for amounts you need to access frequently.
Backup & Recovery
Backup your seed phrase (12-24 words) in multiple secure locations. Never store backups online. From seed phrase, you can recover all funds.
Verify Addresses
Always verify recipient addresses before sending. Use QR codes when possible. Typos in addresses cannot be recovered – funds go to wrong address forever.
Phishing Prevention
Beware of fake wallet websites and emails. Only download from official sources. Check URLs carefully. Cryptocurrency transactions are irreversible.
Two-Factor Authentication
Enable 2FA on all exchange and wallet accounts. Use authenticator apps rather than SMS when available. SMS is vulnerable to SIM swapping attacks.
Challenges & Future Outlook
Current limitations and emerging solutions
⚡ Scalability
Bitcoin processes ~7 transactions per second vs. Visa’s thousands. Layer-2 solutions like Lightning Network enable off-chain scaling without compromising security.
♻️ Environmental Impact
Proof of Work mining consumes significant electricity. This drives innovation toward renewable energy. Proof of Stake alternatives consume 99% less energy.
🎯 Adoption Barriers
User experience complexity deters adoption. Progress in wallet design, payment applications, and merchant infrastructure continues improving accessibility.
📜 Regulatory Landscape
Governments developing cryptocurrency regulations. Some embrace innovation; others restrict usage. Regulatory clarity will likely accelerate institutional adoption.
🔬 Quantum Computing
Future quantum computers could theoretically break ECDSA. Bitcoin community actively researches quantum-resistant cryptography solutions and migration plans.
🤝 Institutional Adoption
Major corporations and funds increasingly hold Bitcoin. ETFs and regulated custody solutions attract institutional capital and improve market maturity.
Visual Representations
2D diagrams showing key concepts
Merkle Tree Structure
Transaction Flow
ECDSA Cryptography
Understanding Cryptocurrency
The Foundation for the Digital Economy
Cryptocurrency represents a paradigm shift in how we think about money and trust. Bitcoin, as the first successful implementation, demonstrates that a trustless, decentralized network can maintain the integrity of financial records through sophisticated cryptography and economic incentives.
While challenges remain in scalability, regulation, and user experience, the core technology has proven robust over 15+ years. Understanding how blockchain technology works—from hashing and cryptographic signatures to consensus mechanisms—is essential for anyone engaging with or investing in the crypto economy.
The future of finance is being written in code, one block at a time.